Table of Contents
Business Email Compromise attacks (BECs)
have been causing organizations problems for years, with the problem getting worse. The reason they’re so difficult to deflect is that, unlike typical email threats, there’s no obvious malware files or rogue URLs for filters to identify. Instead, the messages use social engineering to spoof the sender and duping the recipient into performing an action as they believe the communication is from someone they know and/or trust – such as perform a wire transfer, disclose user credentials or even download malware to infect themselves. According to the FBI, between October, 2013, and December, 2016, the total loss due to BEC crimes was approximately $5.2 billion from over 131 different countries.
In a bid to identify these spoofed messages, email gateway solutions will look for indicators that the sender may not be who they claim to be. However, as many Gmail users found this week, the technology is not infallible with criminals able to exploit a vulnerability that allowed spear-phishing emails to bypass Gmail’s anti-phishing SPF security to land in mailboxes.
Ronald Reagan AttackDubbed the Ronald Regan attack, because they originated from Reagan.com – a legitimate website that allows users to create free email accounts, the malicious BEC emails were sent from an external server but for the end user receiving the message it appeared as if the message had been sent from an internal email account.
The reason these messages were able to bypass the anti-phishing scans in place is due to limitations in the fields that Gmail’s SPF uses to check messages to determine if they are legitimate or not.
This BEC attack is not the first of its kind and is indicative of how new phishing techniques are meticulously designed to bypass secure email gateway technology that relies on outdated rules and signatures instead of understanding behaviors. Many small and mid-sized businesses are highly dependent on Gmail, and trust that the ESP is built to withstand all-types of phishing attacks.
However, as highlighted by developer James Fisher, Gmail’s feature called ‘the dots don’t matter,’ could actually open people up to phishing attacks. I can only assume that the idea behind this is as a benefit to users from mistyped addresses. However, as James’ has highlighted the fact that Gmail recognizes EyalBenishti@gmail[.]com and Eyal.Benishti@gmail[.]com as one and the same is actually a security flaw.
While we all wait to see if Gmail will take action, so that attacks lacking malicious payloads - such as Ronald Regan, can be neutralized before they have the opportunity to cause serious harm, organizations reliant on the service remain vulnerable.
What Is Google Doing About It?
A quick search in Google's reporting system reveals that they don't view SPF vulnerabilities as critical. Therefore, not prioritized to be fixed. If anything changes, we will update this post.
IronSights wouldn’t be Duped
Unlike Gmail, IronSights utilizes UNIQUE anti-impersonation models to detect anomalies and communication habits at the mailbox level. By examining user communications and meta data to establish a baseline, anomalies in communications are easily spotted and automatically flagged as suspicious, to help people make smarter and quick decisions regarding suspicious emails within the mailbox.
In the video below, we show how IronSights would have identified this BEC attack and the information users would have been presented to warn them to the risk.
https://youtu.be/uaxOT0ahTjE
It also explains how IronTraps, our automated phishing incident response solution, could be used to remove duplicate messages for other mailboxes enterprise wide.
Gmail users deserve better as the prevention currently offered simply is not enough. While spoofing and impersonation techniques are becoming increasingly sophisticated, making their authenticity even more difficult to distinguish, its not impossible to determine fact from fiction in the mailbox.
While we wait for other email security solutions to catch on, the only way to reduce email borne threats is to have an automated solution that shifts focus away from the gateway to instead focus on the inbox – where the threat resides.
If you want to stop your organization being duped by scammers give us a call and arrange a demo.
Explore More Articles
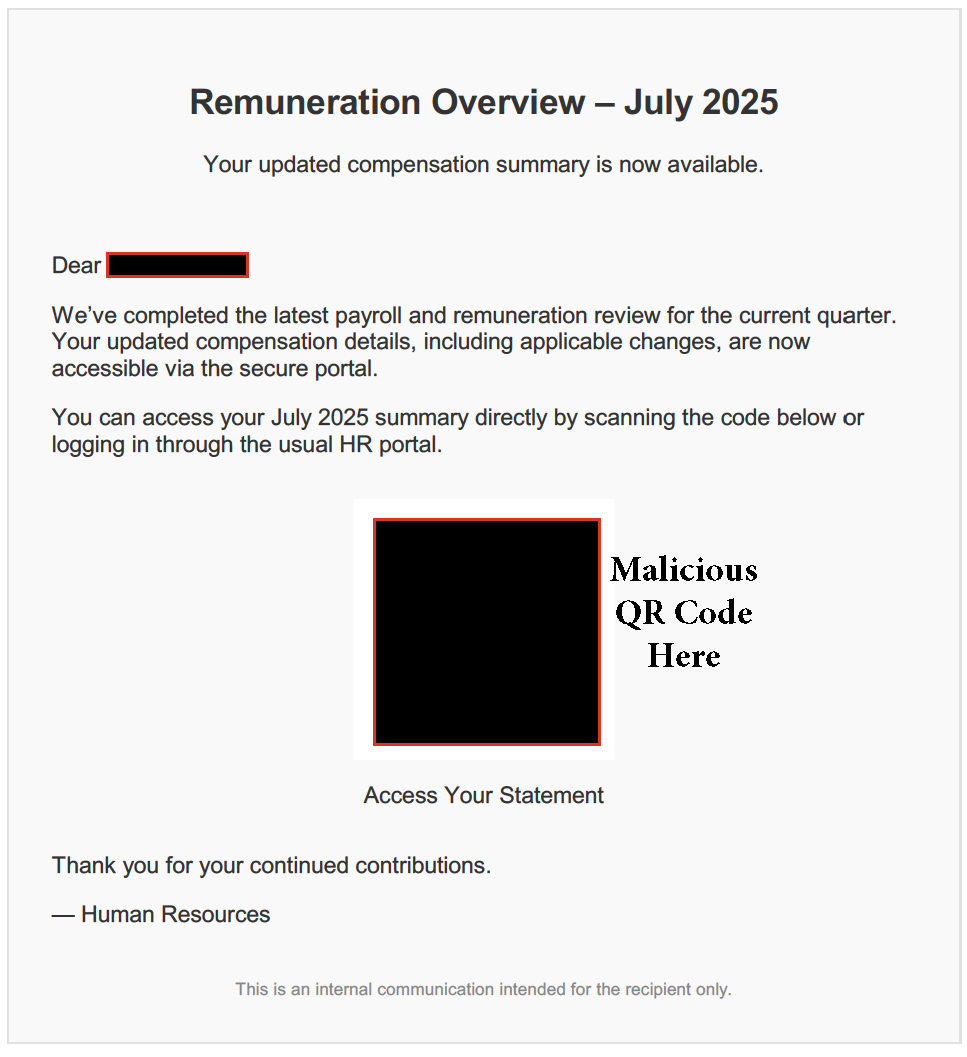
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)









/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)