Table of Contents
Many organizations are reconsidering their email security strategy as they shift from on premise email to cloud-based applications. However, while cloud email systems from Google, Microsoft and others offer consumers built-in security, more often than not such safeguards fail to identify today’s most complex phishing threats.
For example, Microsoft’s cloud-based email filtering system, Microsoft Office 365 Advanced Threat Protection (ATP), has many shortcomings. Most notably, the secure email gateway-like tool relies on human analysts to constantly write rules in response to verified threats. With thousands of attacks targeting Office 365 users daily, it should come as no surprise that it can take Microsoft up to 250 days to create a phishing attack signature. Yet even when signatures are created, they are often ineffective at stopping polymorphic attacks.
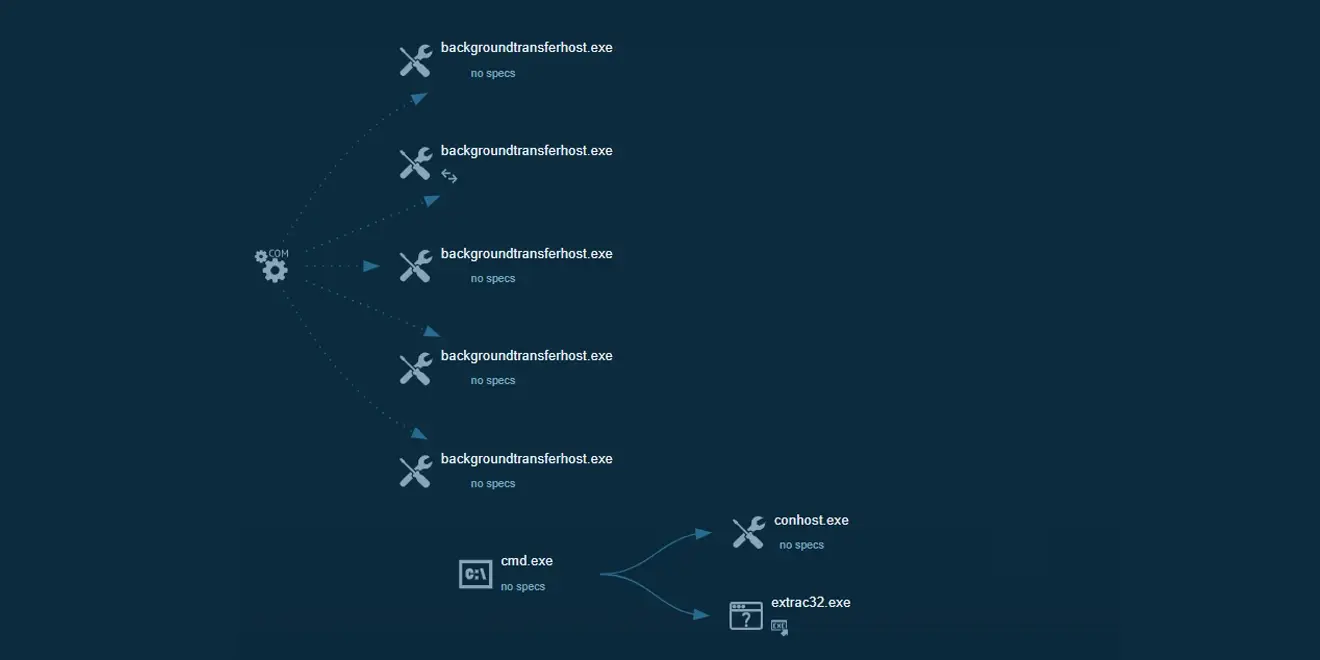
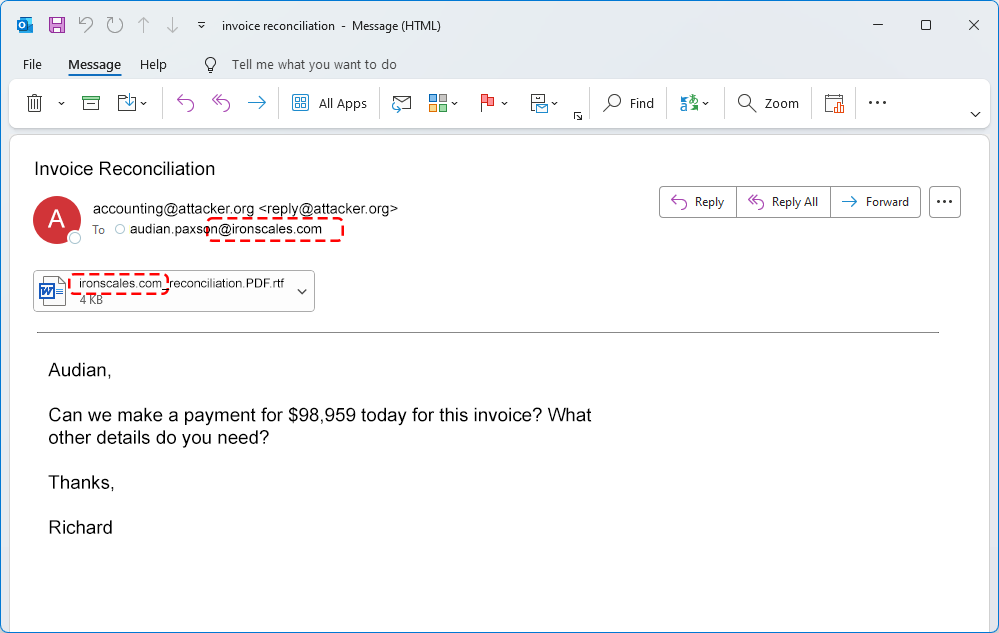
Additionally, and akin to legacy SEGs, ATP operates at the gateway, meaning that it cannot prevent, detect and respond to signature-less attacks, such as fake O365 login pages that attempt to harvest credentials and the various business email compromise (BEC) techniques that are gaining in popularity due to high success rates.
As a result, socially engineered attacks, such as email spoofing, BEC, ransomware and more, are landing in the inbox where tools, such as ATP, are failing to remove threats within the 82 seconds that it takes before the average phishing attack is clicked on. And as we noted in a previous blog post, cunning criminals are even finding ways to bypass more advanced tools such as the new AI filter from Google.
Google and Microsoft have taken steps to invest in strengthening their respective native email security technology, but organizations remain disappointed and thus are looking to supplement elsewhere. Unfortunately, this move brings to light the primary challenge plaguing the email security industry - fragmentated point solutions that operate in silos and only solve small pieces of what is a complex anti-phishing puzzle. From SEGs and spam filters to DMARC, anti-malware and incident response, email security is as complex as any cybersecurity sub-sector. And attackers are exploiting this weakness, resulting in attacks slipping through the cracks.
Now more than ever, CISOs must look beyond siloed protections. They must instead cultivate a unified mindset around email security that integrates prediction, prevention, detection, and incident response. In addition, they must also move towards decentralizing threat intelligence to harness the power of information sharing to reduce risk from advanced attacks.
Taking all factors of email security into perspective
The email security industry’s individual technical controls, aka point solutions, are no longer enough to defend against sophisticated, targeted and advanced phishing attacks. Not only are such solutions insufficient to keep up with today’s emerging threats, but the silos cause friction and additional risk to organizations. After all, what good is having an anti-malware tool and an incident response tool if they cannot communicate with each other seamlessly?
To close these gaps, email security must be holistic, as noted in a presentation given by former Gartner analyst Neil Wynne at the Gartner Risk Summit earlier this summer. Meaning, in order to successfully mitigate risks, an email security strategy must unify users and security teams with an inclusive platform that supports threat prediction, prevention, detection and incident response.
Specifically, during his presentation, Wynne pointed out how users must be at the center of the enterprise email security strategy and that organizations should add layers of detection and response capabilities to catch attacks that can bypass traditional tools. By adopting this mindset, which stems from a continuous adaptive risk and trust assessment (CARTA) model, CISOs can develop a strategic approach to security that uses a continuous assessment of trust and risk through a holistic, unified mindset.
Adding decentralization to the unified mindset
Fortunately, as Wynne point outs, CISOs are starting to understand the need for a unified mindset and embracing platforms, such as IRONSCALES, that bring a more holistic approach to email security. However, one aspect is missing from Wynne’s unified mindset – the idea of decentralization.
At IRONSCALES, we believe in a philosophy of decentralizing email security by utilizing an unlimited network of contributors instead of centralized peers. Our unified platform relies on incident responders, decisions made by our artificial intelligence and machine learning technology as well as the virtual response team of hundreds of thousands of global security analysts. Ultimately, this approach brings together the holistic concept of users and technology controls that Wynne strongly emphasizes as the future of email security.
An added benefit of decentralization is the opportunity it brings to CISOs during their assessment phases, which is the process of outlining their protection architecture and taking necessary steps in making policy changes and reassessing risk prioritization based on threat intelligence shared in the platform. It’s a necessary and vital component to the strengthening email security as outlined by the CARTA model.
Taking the steps to establish a unified mindset is vital for CISOs, SOC teams and security analysts. From new attacks, to gaps in security tools, to moving email to the cloud, today’s changing landscape is putting more pressure on security teams to perform, placing an undue burden that is impossible to meet. By adopting a holistic approach that places an emphasis on uniting technical controls with users – as Wynne points out - organizations will begin to establish a model of assessment that mitigates risk. Only then will organizations truly address the threats and vulnerabilities inherent to email.
Fortunately, IRONSCALES’ long ago adopted this approach by bringing together human intelligence and machine learning technologies into one platform.
To learn more about IRONSCALES and receive a demo on its unified mindset of prediction, detection, prevention and incident response, click here.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)










/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)