Table of Contents
Six months ago we wrote about how ransomware dominated 2017. Six months later, not much has changed.
Despite the regularity of ransomware, it remains a frightening experience to discover that your computer is locked, and a criminal is demanding money to gain access to confidential files. With thousands of successful ransomware attacks perpetrated across the globe every day, holding data for ransom has become a lucrative act for criminals, and a major security concern for businesses. Just ask the city of Atlanta.
According to a report by F-Secure, ransomware attacks grew in volume by more than 400 percent in 2017 compared to the previous year. Much of this was driven by the volume of the WannaCry mass cryptoworm attack which accounted for 90 percent of all ransomware attacks that year.
Due to the reduction in the WannaCry attack, 2018 is so far on pace to have significantly fewer ransomware attacks than last year. However, we're starting to see cybercriminals change their strategies and techniques, focusing less on the “amateurish” ransomware and more on corporate-focused attacks that could compromise organizations through exposed RDP ports. In fact, F-Secure discovered 343 unique families and variants of this kind, more than 60 percent of the number found in 2016.
Big Ransomware Variants Continue to Spread
As ransomware continues to evolve in complexity, it is becoming more difficult than ever for organizations to identify and combat the threats. Instead, many businesses and municipalities are now forced to contemplate whether or not to pay the ransom on an all too frequent basis. Last summer, we took a deep dive into the ransomware families that everyone should be aware of. To help remain current on the threats, we’ve constructed this post with some of the most prevalent ransomware families of 2018, which include:
WannaCry
WannaCry remains the most prolific and destructive ransomware to date. On May 12, 2017, the virus spread rapidly in a mass attack that infected more than 200,000 computers across 150 countries and caused billions in damages. In December 2017, the U.S., U.K. and Australia formally identified North Korea as the culprit behind the attack.
The worm is spread by self-propagation and by taking advantage of a Windows vulnerability that Microsoft (MSFT, Tech30) released a security patch for in March 2017. PC Magazine recently noted that even a year after its major attack, WannaCry persists as many Windows machines across the globe still haven’t installed patches to prevent the attack’s infection method. These untreated machines will carry the ransomware strain indefinitely unless the onboard software is completely reinstalled. Boeing was suddenly hit with ransomware in March, although the vulnerability was limited to a few machines and quickly remediated with a patch, according to the Seattle Times.
SamSam
SamSam is a ransomware strain that spreads through Java apps and targets external-facing RDP servers with brute force techniques to guess passwords to infiltrate networks. Although it has been around since 2015, designers have continually updated it to exploit the latest vulnerabilities in Java-based web servers, FTP servers and other public computer systems. Many attackers search for their perfect targets and deploy SamSam strategically while setting ransoms that are both worthwhile for the attackers and manageable for the targeted organization.
CSO reported that since December 2017, the group behind SamSam has collected nearly $1 million in ransom payments from victims in healthcare, education and government. According to Wired, SamSam struck the City of Atlanta in March 2018 and caused serious disruptions in five of the city’s 13 local government departments.
SynAck
SynAck hit the web last year as another standard ransomware that infects the operating system, encrypts files on the hard drive and then demands money to unlock them. SynAck forces victims to pay in Bitcoin, with ransoms as high as $3,000.
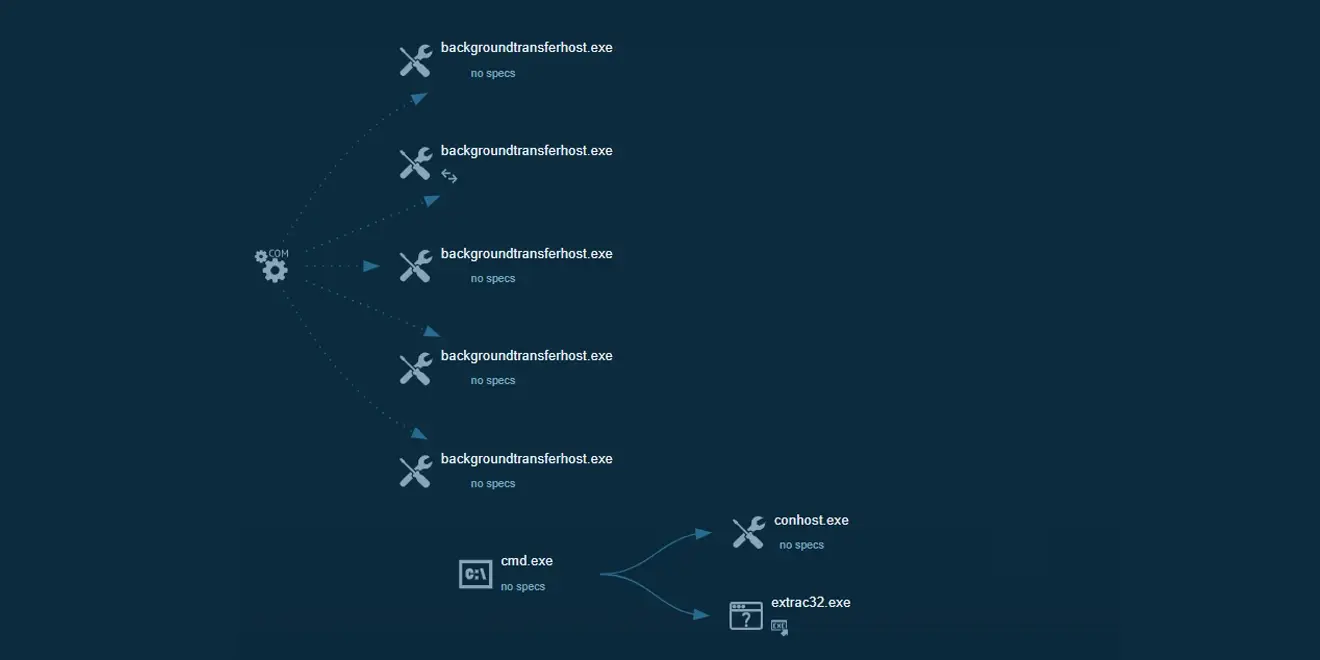
Improved versions of the SynAck ransomware started appearing in the spring of 2018 and now use the Process Doppelgänging technique. This code injection technique takes advantage of Windows mechanisms of NTFS transactions to create and hide malicious processes in a manner that can’t be detected by antivirus software.
Locky
Locky, which we identified and stopped back in 2016, continues to show its ugly head. It spreads through spam emails and social media. Once it infects a machine, Locky scrambles, encrypts with Advanced Encryption Standard (AES) encryption and renames all important files with the .locky extension. The attacker who holds the encryption key for ransom then contacts the user and demands payment. ZDNet called it the “menace that keeps coming back.” Locky plagued the net in 2016, then suddenly disappeared only to re-emerge again in 2017 then again in April 2018 with a new technique that distributed via an infected PDF.
Cerber
Cerber has been around since 2016 and is one of the most easy-to-implement and lucrative ransomware-as-a-service (RaaS) platforms on the market. RaaS makes it possible for any wanna-be criminal to use Cerber through an affiliate program that allows the use of the ransomware in exchange for 40 percent of each ransom paid. While Cerber accounted for as much as a quarter of all ransomware activity in 2017, its threat has since declined. Yet, there are several other variations of similar ransomware that go under different names.
Petya
Last year, many organizations in the U.S. and Europe were hit with the Petya ransomware attack that locked up computers and held data for ransom. The basic MO was to take over computers and demand a ransom of $300 to be paid in Bitcoin. Petya infected computers through the EternalBlue vulnerability in Windows and through Windows administrative tools in addition to other strategies. Security experts said it has a better mechanism to spread itself than WannaCRy.
Petya caused significant disruption at several organizations including French construction materials company Saint-Gobain, Russian firms Evraz and Rosneft and advertising firm WPP. Danish shipping company AP Moller-Maersk, and healthcare facilities in Pittsburgh also reported their systems were hit with Petya.
Preventing Ransomware Attacks With an Automated Phishing Threat Prevention Platform
No one knows what ransomware variations will be victimizing users in the coming months and years. Security used to have a slight advantage over ransomware because it tended to be predictable and worked in a linear fashion. Nowadays, hackers are using tricks to make it less detectable. CSO Online noted some of the biggest ransomware trends for 2018 are to slow down and randomize the encryption process to help avoid detection by anti-ransomware tools.
The good news is that an email security solution to prevent phishing and spear-phishing can also be a strong defense against ransomware. Recognizing the growing number and complexity of ransomware threats in phishing attacks, IRONSCALES’ automatic email phishing prevention, detection and response platform analyzes and responds to threats in real-time. It leverages technical and end-user controls while making users an active part of the defense strategy. IRONSCALES utilizes a bottom-up approach starting at the mailbox level to better understand users’ communication habits while harnessing both human detection and machine intelligence, to automate and respond at scale to these types of attacks. IRONSCALES can be deployed on-premises or via the cloud on both Office 365 and G Suite
Stop phishing and reduce the risk of ransomware. Watch our videos and start using IRONSCALES today.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)










/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)