Table of Contents
In Part 1, I walked through the headline findings from our new research: SEGs are missing an average of 67.5 phishing emails per 100 mailboxes every month.
That stat hit hard. But as we kept talking to security leaders, one question kept coming up:
"Which SEGs are missing the most? What kind of attacks are slipping through?"
Let’s get into it.
How the Major Vendors Compare
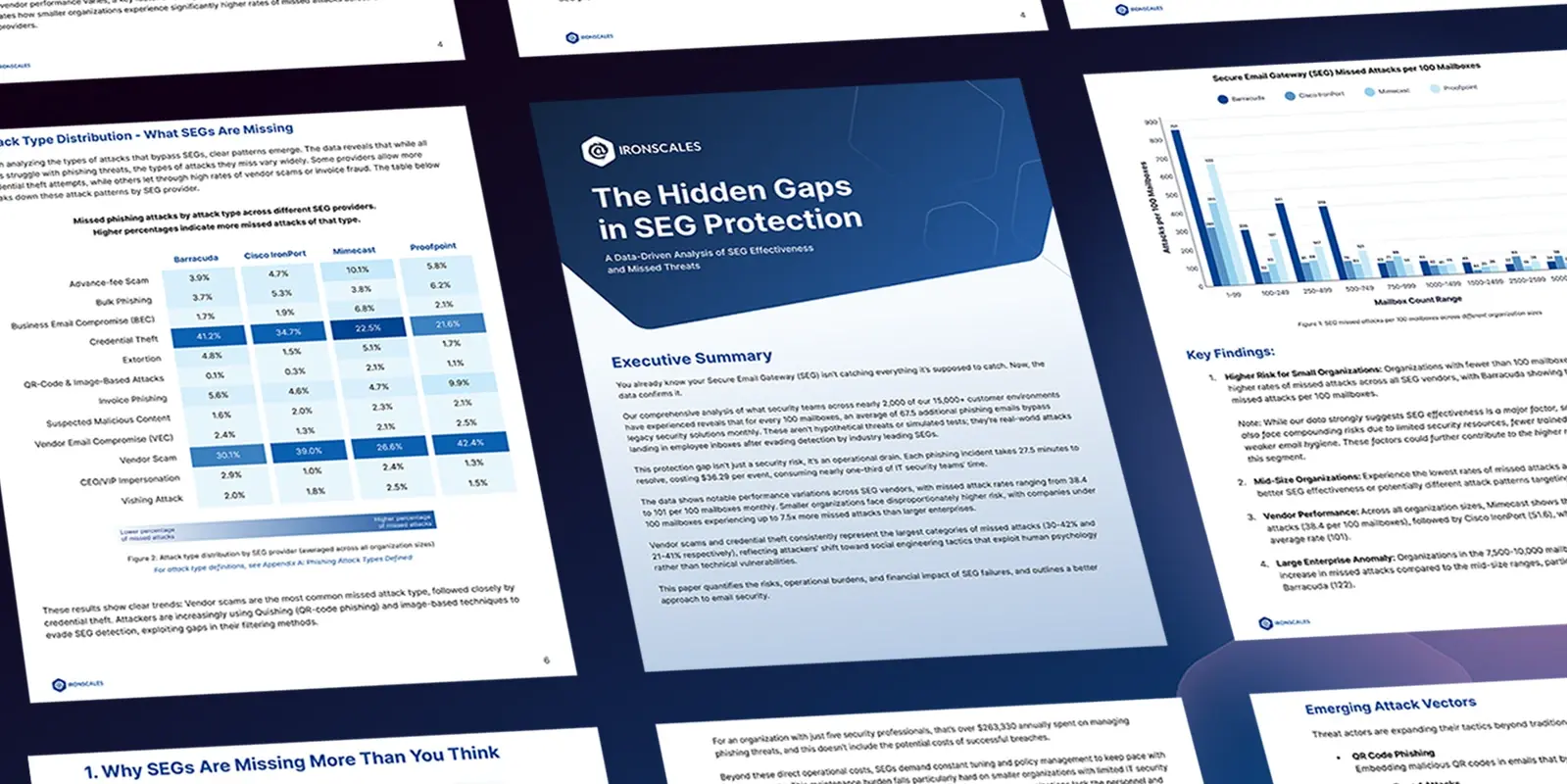
We analyzed real-world detection gaps across four of the most widely deployed Secure Email Gateways: Barracuda, Cisco, Mimecast, and Proofpoint.
Here’s the average number of phishing emails missed per 100 mailboxes per month:
- Barracuda - 101
- Proofpoint - 68.4
- Cisco IronPort - 51.6
- Mimecast - 38.4
These aren't simulations. These are attacks that made it through perimeter defenses and landed in inboxes, where IRONSCALES detected and automatically removed them.
We're not publishing these numbers to shame any vendor. SEGs still play a role in email security. But they're clearly not equipped to stop the kinds of attacks we're seeing today.
What’s Getting Through?
This was one of the most eye-opening parts of the analysis. It’s not just how many phish are missed, it’s what kind:
- Credential Theft
- Vendor Scams (e.g., fake invoices, account updates)
- CEO/VIP Impersonation
- Quishing (QR-code phishing attacks)
- Image-Based Phishing (designed to evade text-based scanning)
- Vishing (voicemail phishing with malware or instructions)
In fact, over 50% of all missed phishing emails across the SEGs analyzed were either credential theft or vendor scams. Note...both of these types of attacks are commonly used in Business Email Compromise (BEC).
Smaller Orgs Are Getting Hammered
Another pattern jumped out: the smaller the organization, the more phishing emails slipped through.
In environments with fewer than 100 mailboxes, we saw miss rates up to 20x higher than in larger enterprises.
Why? A few reasons:
- SEGs often don’t get fine-tuned in smaller environments
- Fewer IT/security resources = less monitoring
- Attackers know smaller orgs are easier targets
And Yes, We Took a Conservative Approach
Now’s a good time to address something a few people asked me after reading Part 1:
“Is this data overstated?”
Actually, no, it’s the opposite.
Some phishing messages land in a gray area, I'm talking about stuff like aggressive marketing or misleading spam. Technically, those could be counted as phish in some detection models. We excluded them.
We didn’t want to inflate our numbers. We focused on clear, malicious phishing attempts. The stuff users click, attackers exploit, and SOC teams scramble to clean up.
Could we have reported even higher miss rates? Yes.
Would that have helped? Probably not.
Instead, we wanted credibility and defensible, real-world insight.
What’s Next?
We've demonstrated that SEGs overlook a significant amount, and the nature of what they miss is crucial. But there’s one attack type we need to zoom in on even more...
Credential Phishing
It’s the second most commonly missed threat across all SEG vendors. And it’s often the gateway to much more serious compromises.
So...in Part 3 of this series, I’ll break down why traditional SEGs are consistently blind to credential phishing (even when those emails look simple on the surface) and what that means for you.
Until then…
...and let’s stop assuming SEGs are enough and start proving what really works.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)