Table of Contents
It was just about one year ago when offices around the world began shuttering, their occupants migrating from conference rooms and cubicles to home office spaces, dining tables, or whatever spot was available between the kids and the cats.
Though it existed long before 2020, the distributed workforce exploded nearly overnight, leaving IT administrators scrambling to ensure their teams had the tools necessary to take care of business as usual.
By most accounts, remote working has proven successful, and will likely be around in some guise for the long term. Businesses in a variety of industries, satisfied by now that productivity levels will not plummet, deadlines can be met, and customers can be cared for, are considering everything from hybrid to fully remote virtual arrangements going forward.
But the COVID-19 pandemic brought more than an embrace of telecommuting to business. It also brought a host of new security threats.
Opening the Remote Office… And the Door to Risk
Those threats result from countless vulnerabilities but can generally be divided into three categories: cloud migrations, human frailties, and malicious actors.
- Cloud Migrations. Many of the tools needed to work remotely – reliably fast internet, presence applications, video conferencing – have been around for years. Others, particularly cloud-based resources, were not as well established but are now seeing significant growth.
Businesses began migrating from premises-based to cloud-based environments about ten years ago. Enterprises were first to take the leap, replacing on-premises data centers and server farms with hosted arrangements, and then cloud infrastructures. Now, with everything from VoIP phone systems to vital business applications in the cloud, organizations large and small alike are moving to the cloud.
In many cases that transition was hastened by the pandemic. To swiftly provide remote teams with the tools needed to work virtually, well planned, long-term migration efforts instead had to be executed much faster. Hurried implementations open the door to minor mistakes or even botched rollouts, which can introduce significant risks.
As if the accelerated pace of migration rollouts wasn’t concerning on its own, there are still very real concerns for some businesses operating in the cloud. Performance issues are not unheard of, and there is some loss of in-house control. It may also be unwise or even forbidden to deploy proprietary technology or store sensitive data in the cloud.
- Human Frailties. Despite the general success of the shift to remote working, teams are still made up of humans, and humans are unpredictable creatures. Working in a home-based environment invites distractions, which means employees may not be paying close attention to suspicious communications. They may be more tempted to use work tools for personal reasons, and adopt a generally casual, laissez faire behavior that puts their employers at greater risk.
According to ResearchandMarkets.com, cybercriminals are taking advantage of this distracted behavior to carry out various phishing scams, some expressly tailored to concerns surrounding COVID-19. And a survey by Tessian found that a staggering 47 percent of respondents cited distraction while working remotely as the reason they fell for a phishing scam.
- Malicious Actors. Finally, there are unavoidable security risks associated with many of the tools that make remote working possible. As the adoption of collaboration tools, file sharing applications, and cloud storage has become more common, cyber attackers have revved up their efforts as well.
In April 2020, still relatively early in the pandemic, Switzerland reported that the number of cyberattacks in that country more than doubled. This was attributed to the increase in people working from home, where levels of protection are typically less than an office environment. The same report noted that between February and May 2020, more than half a million people around the globe had their personal data compromised while using video conferencing services. And from January through June of 2020, the city of London reported that £11 million were lost to COVID-19 scams.
Regardless of the category, without question, the biggest remote working-derived risks to businesses involve email systems.
The Exploitation of Email
From the earliest days of the pandemic, cybercriminals have capitalized on the situation, exploiting both the generally diverted attention of the entire world and the practical shift to remote working. Their activities began early, with email-based attacks and scams recognized as far back as January 2020.
Using COVID-19 as a lure, attack methods have included:
- Business email compromise (BEC): Using COVID-19 to lend gravity to a message, attackers hide behind false contact details to obtain sensitive payroll or banking information.
- Malicious campaigns: In November 2020, TrendMicro reported that strategically timed social engineering tactics were extremely successful with various types of malicious activity.
- Phishing: In March 2020, InfoSecurity Magazine reported that COVID-19 fears drove phishing emails up by a shocking 667 percent. Hackers even used email to impersonate the World Health Organization, hoping to convince individuals to click on malicious links or attachments.
- Ransomware: KPMG noted that working from home significantly increases the likelihood of ransomware attacks given a combination of weaker security controls and higher levels of anxiety. That anxiety leads users to click on COVID-19 lures, including information about vaccines, stimulus payments, and high-demand technology solutions.
Though the major email players go to great lengths to secure their solutions – Google, for example, recognized the danger and acted early in the pandemic – they also make prime targets for cyberattacks. The ubiquity of email, remote working setups that may lack sufficient safeguards, plus potentially distracted and/or naïve employees…for cybercriminals, it is a target far too attractive to pass up.
Protecting Your Remote Organization
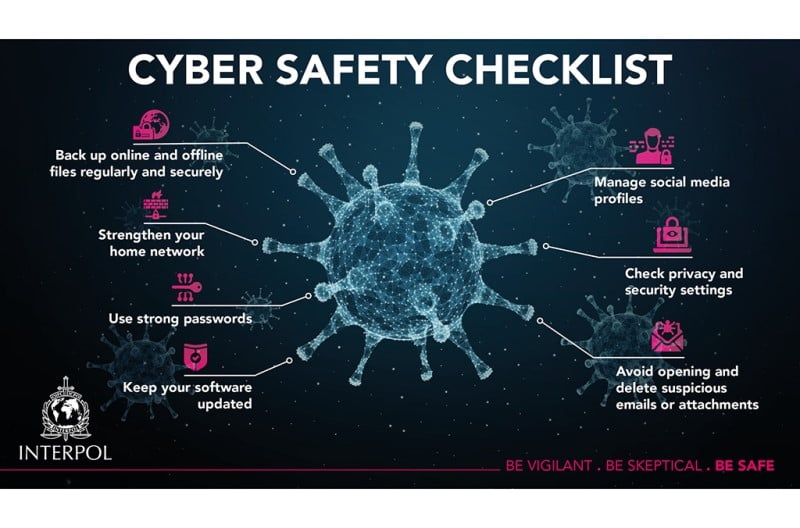
To keep your business safe in the face of increased security threats, international police organization Interpol recommends the following:
Keep your information safe:
- Back up all your important files, and store them independently from your system
- Always verify you are on a company’s legitimate website before entering login details or sensitive information
Check your software and systems:
- Keep the latest anti-virus software installed on computers and mobile devices
- Secure email gateways to thwart threats via spam
- Strengthen home networks
- Secure system administrations vulnerabilities that attackers could abuse
- Disable third-party or outdated components that could be used as entry points
- Download mobile applications or any other software from trusted platforms only
- Perform regular health scans on your computers or mobile devices
Be vigilant:
- Talk to your family − including children − about how to stay safe online
- Regularly check and update the privacy settings on social media accounts
- Update passwords and ensure they are strong
- Do not click on links or open attachments in emails which you were not expecting to receive, or come from an unknown sender
 People-Powered Security
People-Powered Security
To further supplement your secure email gateway, discover how IRONSCALES provides an additional, invaluable layer of security. Our powerful platform helps you defend against threats at your most vulnerable point – your inbox. Contact us to learn more and request a free trial.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)










/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)