Table of Contents
Attack Summary Details
- Impacted IRONSCALES customer mailboxes: 290
- Impacted IRONSCALES customers: 110
- Security Bypass: DKIM
- Technique: Social Engineering
Background
Advanced-Fee Scam attacks are a genre of phishing that was famously made popular by the Nigerian Prince Scam years ago. The schema of the attack is as follows: A recipient receives an email claiming that they have an opportunity to receive funds as a result of some circumstance, usually “inheritances”, “foreign investment” or “lost treasure”. After engaging with a reply email, they are asked to make some up-front payment (frequently in gift cards) in order to receive the promised funds. Once the payment is made the attackers take the money and are never to be heard of again.
The Attack: Method & Payload
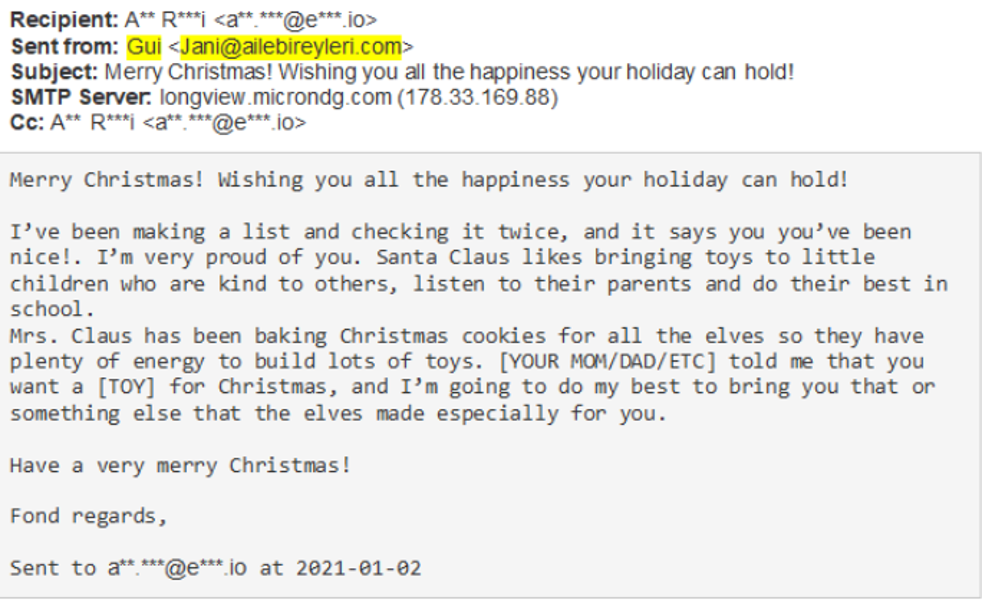
In this attack an email is sent around the dates of the holiday season under the guise of coming from Santa Claus. The recipient is informed that they are to be given gifts as part of the holiday season.
What to Look For
While it may seem that this email is obviously a scam, it is estimated that innocent victims fall to this trap annually, resulting in the theft of hundreds of millions of dollars. Some steps that can be taken to combat such attacks from the user’s perspective are:
- Awareness: becoming familiar with such attack templates and schemas
- Anomaly Recognition: The sender name and sender address in the email do not match, a classic tell of phishing.
How We Spotted The Attack
We were able to spot this attack based on our textual anomaly detection capabilities. Once our platform identified this as a phishing attack, we immediately pulled the emails out of the inboxes of all of our impacted customers.
To learn more about IRONSCALES’ fully integrated anti-phishing and security and awareness training solution, please sign up for a demo today at https://ironscales.com/get-a-demo/.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)









/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)




